Understanding Cybersecurity Guidance: DFARS 252.204-7012, -7019, and -7020
This is an overview of the guidance for Department of Defense (DoD) contractors, focusing on DFARS 252.204-7012, -7019, and -7020, discussing the importance of safeguarding Covered materials.
Introduction
As a technical security professional, you play a front-line role in safeguarding sensitive defense information and ensuring the cybersecurity posture of organizations working with the Department of Defense (DoD). This article aims to deep-dive into the Defense Federal Acquisition Regulation Supplement (DFARS) clauses 252.204-7012, -7019, and -7020, all pivotal in maintaining robust cybersecurity measures and compliance with DoD requirements. By examining the technical aspects of these clauses, you will be better equipped to implement and manage the required security controls, assess risks, and respond to cyber incidents effectively.
The Importance of DFARS Clauses for DoD Contractors
Technical security professionals must appreciate the critical role that DFARS clauses play in safeguarding Covered Defense Information (CDI) and ensuring the security of DoD information systems. These clauses establish a set of security measures and best practices that contractors must follow, providing a baseline level of cybersecurity that minimizes the risk of cyber threats and potential breaches.
To effectively implement and manage the security controls required by the DFARS clauses, professionals must have a deep understanding of the technical aspects of the regulations, the broader cybersecurity landscape, and emerging threats. This includes staying current with the latest industry advancements, monitoring breaking updates to the DFARS clauses, and engaging with industry peers, professional organizations, and cybersecurity experts to share knowledge, best practices, and lessons from real-world incidents.
In addition to understanding the real technical requirements of the DFARS clauses, it is also essential to maintain a holistic view of your organization's cybersecurity posture. This involves routinely collaborating closely with other teams within the organization, such as IT, legal, and procurement, to ensure that all aspects of cybersecurity are addressed and managed effectively in a closed-loop fashion.
Implementing NIST SP 800-171 Security Controls
DFARS 252.204-7012 mandates that contractors implement the security controls specified in NIST SP 800-171, "Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations." These controls are organized into 14 families, including access control, incident response, and system and information integrity. Each family contains multiple controls that outline specific requirements and best practices for securing CDI.
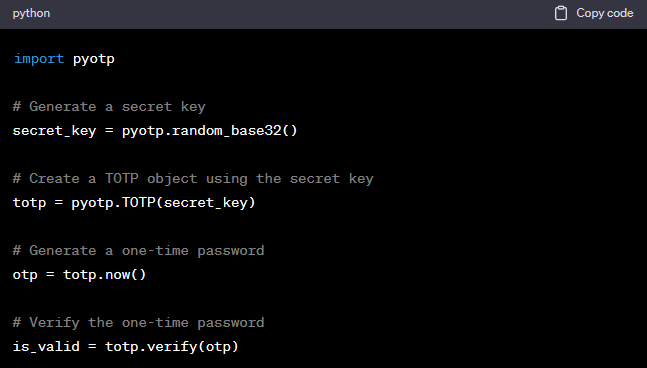
As a technical security professional, you should know each control and its implementation. For instance, when implementing access control measures, you may need to consider control 3.5.3 and configure multi-factor authentication (MFA) for users with access to CDI. Here's a simple example using Python and the PyOTP library to generate a Time-based One-Time Password (TOTP):
This example demonstrates a basic implementation of MFA. Still, tailoring your security controls to your organization's specific workflows and pipelines is essential as part of an overall Shift-left security strategy. Additionally, you should consider the interoperability and integration of various security technologies and the ongoing management and monitoring of these controls.
To ensure the effectiveness of your organization's implementation of NIST SP 800-171, you should also develop and maintain a System Security Plan (SSP) that details how the security requirements are being met. This plan should be regularly reviewed and updated to account for changes in your organization's cybersecurity posture and any updates to the DFARS clauses or NIST SP 800-171.
Suppose your organization cannot fully implement a security requirement. In that case, you must develop a Plan of Action & Milestones (POA&M) outlining the steps to address the deficiency and the expected completion date. This document should be regularly reviewed and updated as progress is made and changes to the security requirements or your organization's environment occur. As a technical security professional, it is essential to collaborate with your organization's leadership and other stakeholders to ensure that resources are allocated effectively and that progress toward addressing deficiencies is tracked and reported.
The Role of Third-Party Providers and Subcontractors
As a technical security professional, you must be aware of the role that third-party providers and subcontractors play in maintaining a secure supply chain. The DFARS clauses apply not only to prime contractors but also to their subcontractors and suppliers who handle CDI. Ensuring that your subcontractors and suppliers maintain robust cybersecurity measures and comply with the DFARS clauses is critical to protecting your organization's sensitive defense information.
To effectively manage third-party risks, you should implement a comprehensive vendor management program that includes conducting regular assessments of your subcontractors' and suppliers' cybersecurity practices, providing guidance on the DFARS clauses, and incorporating contractual requirements that mandate compliance with these regulations. As part of this process, you may need to develop technical tools and methodologies to assess the security posture of your subcontractors and suppliers. This may involve automated vulnerability scanners, penetration testing tools, and other security assessment technologies.
Risk Management and Incident Response
A key aspect of complying with DFARS 252.204-7012 is developing a risk management framework and incident response plan tailored to your organization's needs and capabilities. As a technical security professional, you should work closely with your organization's leadership and other stakeholders to identify potential risks, develop strategies to mitigate those risks and establish procedures for responding to cyber incidents.
Your risk management framework should include periodic assessments of your organization's cybersecurity posture and the identification and prioritization of critical assets that require additional protection. This can be achieved through internal audits, third-party assessments, and penetration testing to identify areas for improvement and ensure compliance with the DFARS clauses. As a cybersecurity professional, you should be well-versed in various risk assessment methodologies and techniques, as well as the tools and technologies that can be used to support these efforts.
Your incident response plan should clearly define roles and responsibilities, establish communication channels, and outline the technical steps to be taken in the event of a cyber incident. This includes procedures for detecting, analyzing, and containing incidents and recovering and restoring affected systems and data. As a technical security professional, you should be proficient in the use of incident response tools, such as Security Information and Event Management (SIEM) systems, Intrusion Detection and Prevention Systems (IDPS), and Endpoint Detection and Response (EDR) solutions, among others.
In addition to developing a comprehensive incident response plan, you should ensure that your organization is prepared to meet the cyber incident reporting requirements outlined in DFARS 252.204-7012. This includes reporting cyber incidents to the DoD within 72 hours of discovery and protecting relevant data for at least 90 days to support potential damage assessments. As a technical security professional, you should know the procedures and tools to preserve and analyze digital evidence and the appropriate channels for reporting incidents to the DoD.
Conclusion
As a technical security professional, your expertise is essential in implementing and managing the security controls required by the DFARS clauses 252.204-7012, -7019, and -7020. By staying informed about updates to these clauses and proactively enhancing your organization's security measures, you can help ensure the protection of sensitive defense information and maintain a strong cybersecurity posture.